DMARC is nothing but Domain-based Message Authentication, Reporting and Conformance (DMARC). DMARC is an email-validation system designed to detect and prevent email spoofing. This is one of the technique used in phishing and email spam, such as emails with forged sender addresses that appear to originate from legitimate organizations.
How DMARC Works?
SPF and DKIM Email authentication protocols were developed more than a decade ago. These provides assurance to receivers to identity of message sender. Even these protocols are already implemented, still there are problems of fraud and spam emails which are not addressed completely. Using spoofing technology, many phishing emails are still receiving by various email users.

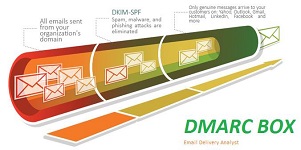
Generally Sender Policy Framework (SPF) are implemented at receiver's end. DMARC is built on top of this mechanism. It allows domain owner to publish a policy on which mechanism (DKIM, SPF or both) is employed when sending emails from that domain and how the receiver should deal with failures. In short DMARC policy allows a sender's domain to indicate that their emails are protected by SPF and/or DKIM, and tells a receiver what to do if neither of those authentication methods passes. These emails can be consider as junk or reject the message. DMARC also report back to the sender's domain about messages that pass and/or fail DMARC evaluation. There are various aggregate reports contain statistical data, while forensic reports can include the message at fault.
DMARC is designed to fit into an organization's existing inbound email authentication process. This helps email receivers to determine the receiving message is from authenticated domain or not. It also provides a reporting mechanism of actions performed under those policies. It thus coordinates the results of DKIM and SPF and specifies under which circumstances the From: header field, which is often visible to end users, should be considered legitimate.
DMARC's validation of the From field has similarities to Author Domain Signing Practices (ADSP, originally called DKIM Sender Signing Practices, DKIM-SSP). The reporting aspect builds on Abuse Reporting Format (ARF). DMARC policies are published in the public Domain Name System (DNS) as text (TXT) resource records (RR) and announce what an email receiver should do with non-aligned mail it receives. DMARC may have a positive impact on deliverability for legitimate senders.
Similar to SPF and DKIM, DMARC uses the concept of a domain owner, the entity or entities that are authorized to make changes to a given DNS domain.
SPF checks that the IP address of the sending server is authorized by the owner of the domain that appears in the SMTP. DKIM allows parts of an email message to be cryptographically signed, and the signature must cover the From field. DKIM-Signature mail header, the d= (domain) and s= (selector) tags specify where in DNS to retrieve the public key for the signature. There may be multiple DKIM signatures on an email message. DMARC requires one valid signature where the domain in the d= tag aligns with the sender's domain stated in the From: header field.
DMARC is producing two types of reports. 1. Aggregate reports, are sent to the address specified under the rua. 2. Forensic reports are emailed to the address following the ruf tag. Multiple reporting addresses are valid and must each be in full URI format, separated by a comma.
DmarcBox Advantages
- 1. DMARC record protects brands by preventing unauthenticated parties/ intruders from using your email domain.
- 2. DMARC reports provides information about who is sending mail from your domain. This provides clear visibility and information about your email outbound IP's .
- 3. DMARC also helps email community and email ecosystem to become more secure and more trustworthy.
